Discovering that someone may expose your intimate images can be overwhelming. Many people panic when they receive a threat or suddenly find a private picture posted online. If you are wondering what to do if someone leaks your private photos, you are not alone. Situations involving online blackmail and image extortion happen more often than people think, and the fear they create can make victims feel trapped or powerless.
Even if “My private photos were leaked” is the thought racing through your mind right now, there are still ways to regain control. Acting quickly can reduce the spread of a leaked photo and improve the chances of removal. This guide explains what to do if someone is leaking photos of you online, including practical steps to protect yourself, report the content, and stop the situation from escalating.
What If Someone Leaks Your Private Photos or Threatens To?
People usually arrive at this situation in one of two ways. Either someone is threatening to release their images, or the photos have already appeared somewhere online. Both cases are stressful. Still, the response should remain calm and methodical. Online blackmail often follows predictable patterns, and recognizing the situation early can help you react more effectively. Understanding how these situations develop also helps victims avoid mistakes that make the problem worse.
When Someone Threatens to Leak Your Photos
Threats often appear during sextortion or relationship-related conflicts. A scammer or former partner may claim they will send images to your friends, workplace, or family unless you give in to their demands. In many sextortion cases, the criminal does not know the victim personally. They rely on panic to force quick payments.
For example, a common sextortion scam begins after someone meets a stranger on a dating platform or social media. The conversation moves to a private video chat. The scammer records the interaction and then sends screenshots as proof. Within minutes, they demand payment and threaten to share the recording publicly.
This tactic is widespread. The FBI reported receiving 54,036 sextortion-related complaints in 2024, a 59% increase in complaints from 2023. Many victims were targeted through social media or messaging apps.
When Private Photos Are Already Leaked Online
Sometimes victims only discover the problem after a leaked photo appears online. This can happen after a relationship ends, after a hacked account, or when someone secretly shares images without consent. The content may appear on social media, forums, group chats, or anonymous websites that distribute private images.
One widely discussed example involved stolen celebrity images that spread rapidly across forums and file-sharing sites. That incident showed how quickly private content can circulate once it reaches public platforms. Even though the circumstances were different from personal sextortion cases, it demonstrated how quickly images can travel across the internet.
If you are dealing with a situation where nudes leaked online, what to do becomes the urgent question. The most important thing to remember is this: Immediate action matters. Collecting evidence and reporting the content quickly can significantly reduce how widely the images spread.
What to Do if Someone Is Threatening to Expose You
Dealing with threats of exposure is a serious matter that can significantly impact your mental, emotional, and physical well-being. However, it is important to remember that you have options. Even if exposure has not occurred, the threat itself is still a crime in most jurisdictions. The first step is to gather evidence of the threat. This could include documenting details such as account information, threatening messages, and time stamps.
Next, you are going to want to report this crime. You can report this crime to the platform on which the threats are being made, the FBI’s Internet Crime Complaint Center, and your local law enforcement. It is also crucial to seek support from friends, family, or professionals who can help you through this difficult time. Finally, consider speaking to a legal expert who can guide you on the best course of action. Remember, being threatened with exposure does not define you, and help is available if you need it.
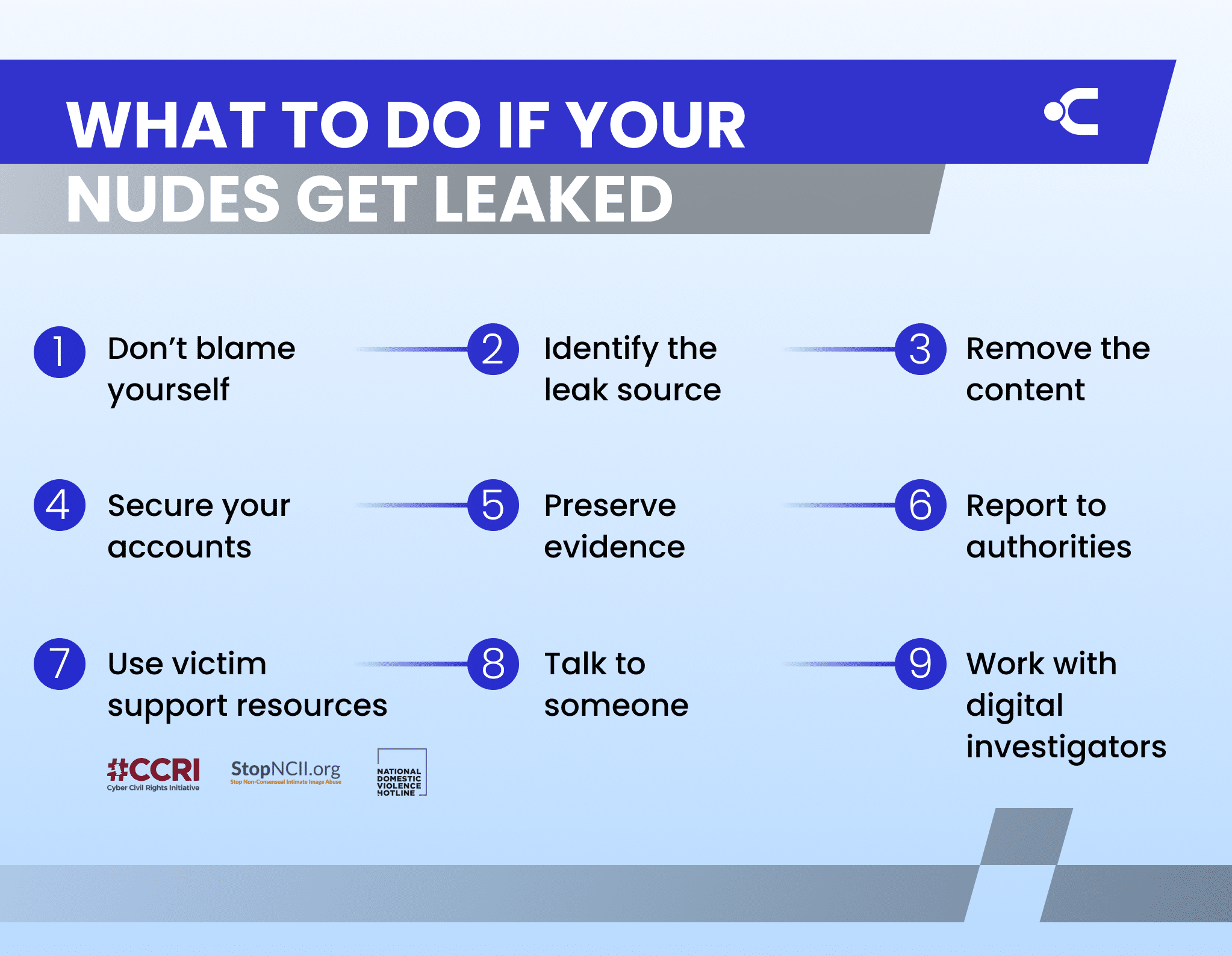
Immediate Steps to Take If Your Private Photos Are Leaked
Once you realize someone is threatening you or sharing your images online, your first reaction might be panic. That reaction is normal. Still, the actions you take in the first few hours often determine how much control you can regain. Many victims who respond quickly are able to limit how widely a leaked photo spreads and remove it faster.
Below is a practical response plan used by investigators and cybercrime specialists.
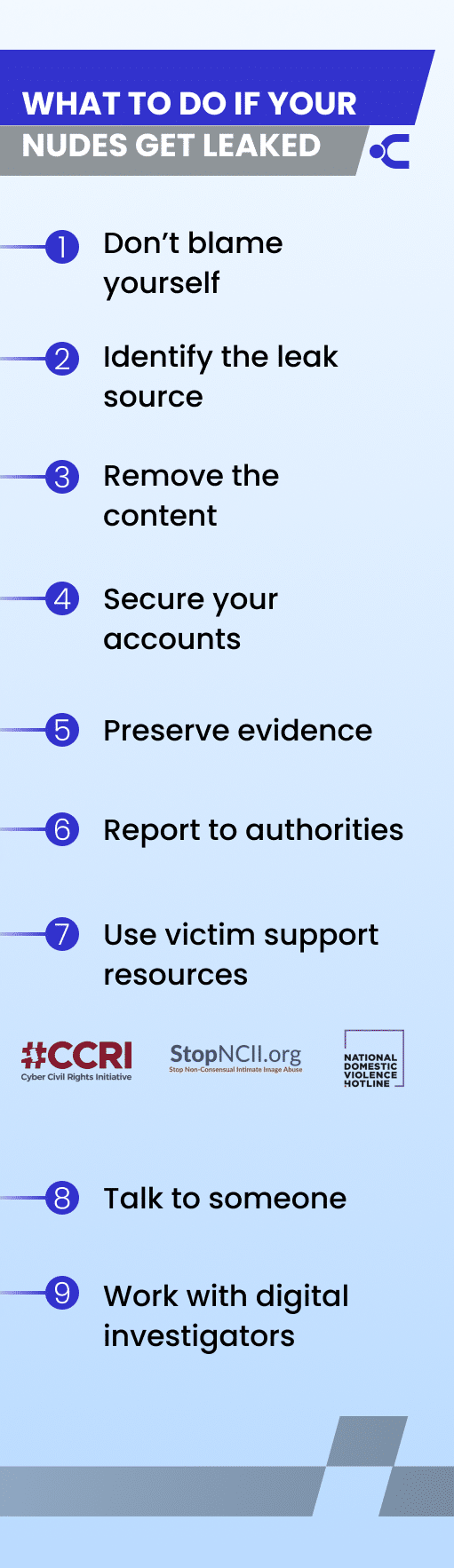
Stay Calm and Do Not Blame Yourself
Revenge porn is a crime and a complete betrayal of trust. However, it’s normal to feel guilty after being betrayed. Victims often blame themselves when their nudes are leaked. However, it is never their fault that someone else invaded their privacy. The criminal is at fault, not the victim.
Blackmailers rely on fear. They want victims to react quickly and make decisions without thinking. They often send countdown messages or aggressive warnings to create pressure. Avoid paying money or sending more images. In many cases, payments do not stop the threats. Criminals frequently return with new demands after receiving money.
For example, several sextortion cases reported in the United States involved victims paying hundreds of dollars, only to receive additional threats days later. Even when victims agree to pay, the threats usually continue. Studies suggest that between 27% and 50% of victims who send money are contacted again with new demands. The safest move is to pause, avoid emotional responses, and begin documenting the situation.
Assess Where the Leak Came From
Before you can take steps to protect yourself, you need to identify where the leak came from. Common perpetrators of NCII abuse include former partners, online acquaintances, or complete strangers. Based on the content that was shared, along with other contextual details, you can narrow down the potential source.
Former partners usually include specific details and are typically motivated by emotion rather than financial gain. On the other hand, threats from strangers are often vague and include pressure tactics and urgent language with the intent to extort money. While these characteristics do not guarantee the source, they can help you choose the proper steps to protect yourself.
Request Removal from Search Engines
Even after a post is removed, search engines may still show cached links or preview images. This can make it seem like the content is still circulating widely. Search engines allow victims to request removal of sensitive personal images from results. Google, for example, accepts requests for the removal of non-consensual explicit images.
Another option is filing a DMCA takedown request if the photo belongs to you. This process asks websites and search engines to remove copyrighted content that was shared without permission. Removing search listings does not always erase the image everywhere. However, it dramatically reduces visibility and makes the content much harder for others to find.
Update Your Privacy and Security Settings
The uncertainty around how your nudes were leaked highlights the importance of victims securing their accounts and devices to protect themselves from further abuse. Making your online profiles private can help prevent strangers with harmful intentions from targeting you.
You should also enable two-factor authentication wherever possible. This setting can prevent account takeovers — even if your login credentials are compromised. The cornerstone of online security is passwords. In the modern age, passwords need to be complex and unique to keep your information safe.
Collect and Preserve Evidence
Before reporting the incident, gather as much information as possible. Evidence strengthens removal requests and helps investigators track the person responsible.
Save the following:
- Screenshots of threats or messages
- Usernames and account profiles
- Links to posts or websites hosting the images
- Timestamps showing when the threats happened
- Copies of emails or chat conversations
Do not edit or crop screenshots if possible. Full captures often show details such as account names or timestamps that become useful later. Some victims skip this step because they don’t want to revisit the abuse. However, proper documentation often becomes the strongest tool when trying to report leaked photos or file a legal complaint.
Report the Leaked Photos to the Proper Authorities
You should report the threats and any instances of exposure to the online platform where it occurred. Most major platforms have strict rules against non-consensual intimate images. Once reported, moderators can remove the content and take action against the account.
Additionally, reporting NCII abuse to the authorities is always recommended. Your local police can help you file an official report that includes your collected evidence and helps build a case against the cybercriminal responsible. If the crime exceeds their scope of jurisdiction, they can help advise you on your next steps.
The FBI operates the Internet Crime Complaint Center (IC3), the national hub for reporting cybercrimes. Filing a report to the IC3 not only helps the FBI track national cybercrime trends, but they can also collaborate with international law enforcement agencies to pursue perpetrators — even if they are located outside of the U.S.
Use Victim Support Resources
There are many non-profits and online tools created to support victims and provide help on what to do if someone shares their nudes. Here are the main resources to look into:
- Cyber Civil Rights Initiative: A non-profit that supports victims of NCII with legal guidance, a 24/7 hotline for emotional support, and educational resources.
- StopNCII.org: A global tool that helps victims remove NCII and mitigate its resharing through hash-based matching.
- National Domestic Violence Hotline: A free and confidential service that focuses on domestic abuse but also supports victims of NCII abuse.
Talk to Someone
Being a victim of NCII abuse can be devastating on many levels. There is a lot of distress, fear, anger, and anxiety that can come from being exposed. However, what can make things harder is facing all of it alone. Talking to someone during this experience can alleviate the overwhelming emotions you are feeling. It can also help calm your mind, allowing you to make informed decisions. This person can be a trusted friend, family member, therapist, or advocate at a non-profit.
Identify the Perpetrator with Digital Investigators
The criminals responsible for NCII abuse tend to hide behind anonymity. This protects them from being held accountable and allows them to operate in secrecy. However, cybersecurity experts can investigate anonymous incidents and trace the exposure back to its original source. Using digital forensics, they can analyze the digital footprint to reveal the culprit’s geolocation and, in some cases, their identity. The findings from the digital investigation can be used as evidence in court proceedings against the offender.
Taking Care of Your Mental Health If Private Photos Were Leaked
When private images are leaked or used for blackmail, the emotional impact can be just as serious as the privacy violation. Many victims experience stress, embarrassment, anxiety, or fear about how others may react. These reactions are normal. Protecting your mental health is an important part of recovering from the situation.
Several trusted organizations in the United States provide free support and confidential guidance. Consider the following resources:
- 988 Crisis Lifeline: Call or text 988 or chat online to reach trained counselors anytime. The service provides free and confidential emotional support 24/7.
- Crisis Text Line: Text HOME to 741741 to connect with a trained volunteer counselor through confidential text messaging support available around the clock.
- National Alliance on Mental Illness: Provides mental health information, emotional support, and resource referrals through phone, text, or online chat.
- FindTreatment.gov: A government tool that helps people locate mental health and substance use treatment services across the United States.
Remember that the responsibility for the situation lies with the person who shared the images without consent. Seeking help, speaking to supportive people, and using trusted mental health resources can make the recovery process much easier.
How to Prevent Future Leaks and Image Extortion
While the responsibility always lies with the person who shares images without consent, strengthening your digital habits can reduce the chances of similar situations happening again. Many cases of image extortion begin with strangers gaining trust online or accessing private accounts through weak security. A few preventive steps can make a significant difference.
Here are practical precautions that help protect your privacy:
- Use strong and unique passwords for every account. Avoid reusing passwords across social media, email, and messaging platforms. If one account becomes compromised, others remain protected.
- Enable two-factor authentication on important accounts. 2FA adds an extra layer of security. Even if someone obtains your password, they cannot access the account without the second verification code.
- Be cautious when sharing intimate images online. Once a photo is sent digitally, control over that file becomes limited. Even trusted contacts can lose devices, experience account hacks, or accidentally expose private content.
- Verify identities during online conversations. Many sextortion scams begin with fake profiles. If someone pushes for private photos or video calls quickly, that is often a warning sign.
- Secure your cloud storage and private galleries. Photos stored in cloud services should be protected with strong passwords and account recovery settings.
- Keep social media profiles private when possible. Limiting who can see your posts and personal details reduces the chances that strangers collect information for blackmail attempts.
Why Professional Help Matters
Handling a leaked image situation alone can be exhausting. Victims often spend hours reporting posts, searching for copies, and trying to contact websites that may not respond quickly. In many cases, the person responsible continues creating new accounts or reposting the same content on different platforms. When this happens, professional support can make the process faster and more organized.
Digital investigators and content removal specialists understand how these cases typically unfold. They know where leaked images often appear and how different platforms handle abuse reports. Instead of submitting one report at a time, professionals can identify multiple locations where the image is hosted and start coordinated removal requests.
Professional assistance may include:
- Tracking where the image appears online. Investigators use monitoring tools to locate reposts across social media, forums, and file-sharing platforms.
- Submitting structured takedown requests. Experts prepare reports that include the correct documentation, links, and evidence required by platforms and hosting providers.
- Preserving digital evidence. Properly collected evidence can become important if the situation escalates into legal action.
- Helping stop continued harassment. If the same person keeps reposting images or sending threats, investigators can document the pattern and help escalate the case.
Many victims feel relief once an experienced professional begins handling the technical side of the situation. It allows them to focus on recovery while the removal process moves forward.
Get Help If Someone Leaks Your Private Photos
If you discover a leaked photo, do not hesitate to seek support. Situations involving what to do if someone is leaking photos of you online often require persistence, but removal and resolution are possible.
If you need help stopping image extortion, tracking where images appear online, or requesting takedowns across multiple platforms, contact Cyber Investigation for expert guidance. Cyber Investigation has a team of cybercrime experts who know exactly what to do if your nudes are leaked.
Using state-of-the-art technology, we can follow the digital trail of NCII abuse to its original source through methods like metadata analysis and IP tracking, which can help uncover the criminal’s geolocation. From there, we can work to identify the perpetrator. This information can help you pursue legal action and hold the threat actor accountable.
We also work quickly to remove any private content that was posted online without your consent and offer an ongoing monitoring service that tracks any further postings after the initial incident has been handled. At Cyber Investigation, we provide all of this and more to protect your online reputation and mitigate any damage from exposure. You don’t have to experience this alone. Reach out Our Sextortion Helpline today and let our experts help you through it.