If someone is threatening you online or demanding money, you’re not alone. Learn what to do, how to protect yourself, and how our experts can help stop extortion quickly. Get confidential help from Cyber Investigation today.
Online Extortion Is More Common Than You Think
If someone is trying to extort you online, the first reaction is often fear. Many people feel confused and unsure what to do next. These threats are designed to create pressure and force quick decisions. The person may demand money, property, or some form of action.
These schemes can happen through email, social media, or messaging apps. They utilize social engineering tactics to produce a sense of urgency and seriousness. If you are searching for what to do if you are being extorted, it’s important that you do not panic or pay. Quick reactions often make things worse.
What you need is an informed, expert-guided response. There are clear steps you can take right now to protect yourself and stop the threat from growing. To achieve this, you need to know what online extortion is, how these scams unfold, and who you should turn to for help. Keep reading to learn what you should do next.
What Is Online Extortion?
Online extortion is when someone uses fear or pressure to force you to give money or comply with a demand. The threat is delivered through digital channels. Scammers gather leverage through manipulation tactics, previous data breaches, hacking, or publicly available information.
If you’re being extorted for money, you are not alone. Many people face this each day through email, social platforms, or direct messages. In some cases, the threats are generic and sent to multiple users at once. However, some are calculated attacks tailored to a specific target.
Unlike blackmail or sextortion, online extortion does not focus solely on private or personal content. It is a broader crime based on threats, claims, or pressure of any kind. Here are some real situations that reflect how this works:
- An unknown sender emails you and claims they will post false accusations about you unless you send Bitcoin. This type of message has been widely reported and often includes emails that are sent in bulk.
- A small business owner receives a message saying bad reviews will be posted across platforms unless a payment is made. Being extorted for money as a business owner can threaten your long-term reputation and livelihood.
- A person claims they have hacked your system and stolen your files. They demand payment to avoid exposure. Some of these claims end up being false, but the existence of legitimate hacking attacks demands a serious response to such threats.
- A fake account reaches out on social media and says they will report or harm your account unless you pay. Many users who are being extorted for money report this type of message on platforms like Instagram or Facebook.
- A caller claims to represent a group and threatens legal or public action unless funds are sent quickly. Victims who are being extorted for money often receive repeated calls or follow-up messages.
If you are thinking, “I’m being extorted for money,” pause and assess the situation. These threats can come through any communication channel, and anyone can be targeted. The method may change, but the pattern stays the same.
People who are being extorted for money often notice one thing in common. The sender creates urgency and fear. That is the main tactic. If someone is trying to extort you for money, focus on facts, not fear.

Common Online Extortion Scenarios
Online extortion does not always look the same. The message, the platform, and the story may change, but a similar fundamental structure remains. A threat is made, pressure is applied, and payment is demanded. If you are trying to understand how to deal with online extortion, it helps to recognize how these situations usually appear.
- One common method starts with a simple email. The sender claims they have access to your system or personal data. They demand payment to prevent the release of your data and set a short deadline to create urgency.
- Social media is also a frequent channel. A fake account may contact you and claim to have reported your profile or gained access to your content. They then ask for money to “fix” the issue.
- Some users receive messages through apps like Skype or Facebook. The sender claims to be part of a group and threatens legal or public action. They push for quick payment and repeat the message if ignored.
- There are also cases where a person claims to have stolen business data or client records. They demand payment to avoid sharing it.
If any of these sound familiar, you are not alone. These patterns are well known, and there are safe ways to respond. If you need online extortion help or want to understand what to do if you’re being extorted, you can read a more detailed guide here.
Step-by-Step: What to Do If You’re Being Extorted Online
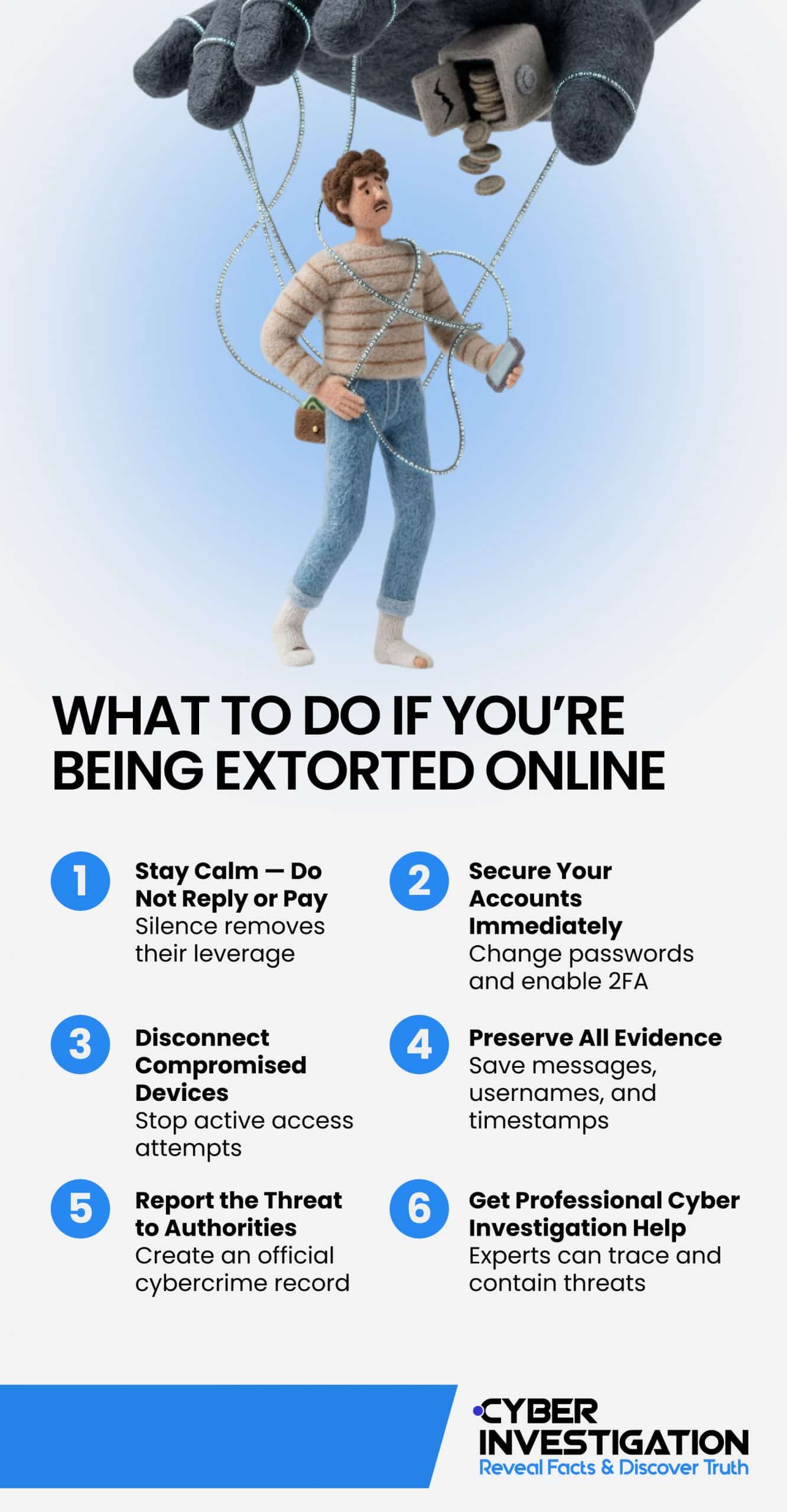
If you are searching for what to do if you are being extorted online, start with calm and clear action. You are not powerless. These steps help you take control and reduce risk.
- Stay calm and do not reply or pay. The message may feel urgent. That is how pressure is created. Do not respond and do not send money. Payment does nothing constructive to end the threat and often leads to more demands.
- Preserve all evidence. Save everything you receive. Take screenshots of messages, emails, usernames, and any other relevant data. Keep links and timestamps. This helps track the source later.
Do not delete messages — evidence is critical for tracing and legal reporting.
- Secure your accounts. Change your passwords right away. Use strong and unique passwords for each account. Turn on two-factor authentication and enable heightened security settings. Check login history and remove unknown devices.
- Disconnect any hacked devices. If a threat claims access to your system, scan your device with reputable security tools. If needed, disconnect the device from your network and seek technical support.
- Report the threat. You can report to your local cybercrime unit. In the United States, the Internet Crime Complaint Center (IC3) is the FBI’s reporting channel. This step is key if you are unsure what to do if you’re being extorted.
- Get professional help. Cyber investigators can review the threat, trace digital activity, and guide safe next steps. If you are still wondering what to do if you are being extorted, expert support can help guide you through the process.
Real-World Examples: How Online Extortion Happens
Freelancer Targeted with Fake Client Review Threat
A freelance designer received an email from someone claiming to be a past client. The sender said they would post negative reviews across job platforms unless a payment was made. The message included deadlines and repeated follow-ups. The freelancer began to think, “Someone is trying to extort me online.”
As the tone became more aggressive, no real proof of past work was provided. Cyber Investigation reviewed the case and retrieved evidence that assisted efforts to determine the legitimacy of the threat. Our analysts preserved all communication, tracked the source pattern, and guided the freelancer on how to properly handle the incident.
Small Business Receives Bitcoin Demand Email
A local business owner received an email claiming that false news articles would be published about their company unless a Bitcoin payment was made. The message looked formal and used urgent language. The owner felt pressure to act fast.
Cyber Investigation assessed the email and found it matched known mass extortion patterns. The same message had been previously reported by other business owners online. Our team helped collect evidence, secure business accounts, and prepare a report for authorities while ensuring no further engagement with the sender.
Instagram Impersonator Demands Payment
A user reported being extorted on Instagram after receiving messages from an account using their name and photos. The impersonator claimed they had access to private content and demanded money to delete it. The victim feared damage to their online presence and asked what to do next.
Cyber Investigation analyzed the account and interaction to uncover evidence that was used to identify the perpetrator. They documented the messages, reported the account through proper channels, and guided the user on securing their profile and preventing further impersonation attempts.
Why You Shouldn’t Pay an Extortionist
Payment Rarely Ends the Threat
Paying an extortionist may feel like the fastest way to stop the situation, but it rarely works that way. In many cases, the first payment leads to more demands. The sender now knows you are willing to respond. If you are thinking, “I’m being extorted for money,” it is important to understand this pattern. These threats are built to create urgency and fear. Once you pay, the situation often escalates instead of ending. Learning how to deal with online extortion helps you avoid falling into repeated demands and ongoing pressure.
Payment Confirms Willingness to Comply
When you send money, you confirm that the pressure is working. This makes you a more attractive target for the same sender or even others. Many people who say, “I’m being extorted for money,” report that the demands increased after they paid once. The amount may go up, or new threats may be introduced. This cycle can continue if the sender believes you will keep responding. Knowing how to deal with online extortion allows you to break this pattern early and avoid further contact or escalation.
There is a Safer Way to Handle It
Instead of paying, there are structured steps that help you take control of the situation. Securing your accounts, saving evidence, and avoiding contact can reduce risk. If you are unsure what to do, professional support can guide you through each stage. Cyber investigators assess the threat, track digital activity, and manage communication safely. If you are dealing with a situation where you’re being extorted for money, following the right process is far more effective than reacting under pressure.
Contact Us and Stay Safe
If you are facing an online threat, you do not have to handle it alone. The right support can help you stay in control and respond safely.
- Threat assessment and source tracing. Every case starts with a detailed review of the threat. Our investigators examine messages, email headers, and digital activity to identify patterns. We work to trace the sender through IP data, device signals, or crypto wallet activity. This step helps you understand who is behind the threat and how to stop extortion safely.
- Digital evidence collection. All communication is preserved in a structured way for further action. This includes screenshots, logs, transaction details, and account data. Proper documentation strengthens your case if you decide to report it. It also ensures that no critical detail is lost during the process.
- Safe communication management. Direct contact with an extortionist can make the situation worse. Our analysts can guide you on when to respond and when to stay silent. In some cases, we can manage communication to control the situation. This reduces risk and prevents further pressure from the sender.
- Reputation and data protection. Steps are taken to protect your online presence and limit any possible damage. This may include account security, content monitoring, and quick response actions. If false claims or threats are involved, they are handled with care. The goal is to keep your personal or business reputation stable.
- Legal coordination. If needed, investigators help prepare your case for formal reporting. They assist with filing complaints and sharing evidence with the right authorities. This makes the process easier and more structured. It also improves the chances of proper action being taken.
Our investigators combine digital forensics, intelligence tools, and discretion to protect your privacy and stop the threat. If you need online extortion help or want to understand how to stop extortion, do not try to manage it alone.
If you are dealing with a situation where you are unsure about how to deal with online extortion, the right support can make a real difference. Acting alone can increase stress and lead to mistakes, while expert guidance helps you stay in control. If you’re being extorted or threatened online, Cyber Investigation can help you collect evidence, report the threat, and stop it safely.
Frequently Asked Questions
What to do if you are being extorted on Snapchat?
Stop replying and do not send money. Save chats, usernames, and screenshots, then secure your account and report the profile through Snapchat.
What if you are being extorted on Skype or Teams?
End communication and document all messages and call details. Report the account, check your device’s security, and seek help if the pressure continues.
What to do if you are being extorted on Instagram or Facebook?
Report the account right away if you are being extorted on Meta platforms. Save all evidence and review your privacy settings to prevent further contact or impersonation.
What happens if you pay an extortionist?
Payment often leads to more demands instead of ending the threat. Many victims who are being extorted for money report repeat requests after the first payment.
What is a webcam extortion scam?
It is a scam where someone claims to have recorded you and demands money to prevent release. These threats are often false and rely on fear to force payment. However, you should still treat them seriously and investigate them properly.
If you are extorted, when should you contact the police or authorities?
You should report the situation when there are direct threats to cause physical or reputational harm, especially when they include financial demands. Even if threats haven’t been made, you should report any unwanted contact that continues despite your requests for it to stop.
You should file a report through your local and national cybercrime units’ official channels. If you need expert support, Cyber Investigation can help gather digital evidence to support your case.