Learn how to report cyber harassment, gather evidence, protect your accounts, and stop online abuse. Step-by-step guidance, prevention tips, and expert support.
41% of all adults in the United States have experienced online harassment. In the under-30 age range, that percentage jumps up to 64%. And yet, it’s estimated that between 60 and 90% of harassment cases go unreported. Many victims feel too afraid or ashamed to come forward, but silence only perpetuates the cycle. It’s important that all internet users know how to report cyber harassment, but many don’t know where to start.
Understanding how to report cyber harassment is not just about taking action, but about protecting yourself, building a strong case, and stopping the abuse early. Whether the harassment happens on social media, messaging platforms, or forums, the response process remains similar. This guide walks you through what qualifies as harassment, how to collect evidence properly, and how to start the reporting process with clarity and confidence.

What is Cyber Harassment?
Cyber harassment is defined as the use of electronic communication with the intent to harass or intimidate another person, causing emotional harm or distress. There are multiple means of communication through which cyber harassment can occur, such as email, social media, dating sites, and other platforms.
Harassment is legally defined as unwanted words or behavior that threatens, intimidates, or demeans someone else to cause emotional distress. Cyber harassment follows the same definition but occurs through digital channels.
The severity of harassment ranges from physical threats to name-calling. In any case, the prevalence of online harassment has continued to grow over the years. Now, internet users need to be aware of the risks and how to stop online harassment if they are ever targeted.
Types of Cyber Harassment
Internet harassment can take many forms, from mild annoyance to serious criminal behavior. The following are some of the more common forms of cyber harassment to look out for:
- Cyberbullying: The use of electronic communications to humiliate, harass, or intimidate another person. Cyberbullying can range from general gossip to severe defamation.
- Doxxing: The act of publicly revealing someone else’s private information without their consent. The victim may be identified through this information, which can put their online and real-world safety at risk.
- Threatening Messages: Verbal, electronic, or written communications that intend to intimidate, harm, coerce, or manipulate the recipient.
- Cyberstalking: The use of electronic communication to harass or threaten another person in a manner that causes the victim to fear for their safety or suffer distress.
- Trolling: Inflammatory, disruptive, or provocative internet behavior with the intent to upset or anger others.
- Revenge Porn: The non-consensual distribution of intimate images or videos of someone else, causing emotional distress. In many jurisdictions, there is a requirement to prove intent to cause harm.
- Verbal Harassment: Using words to offend, intimidate, or harm another person, causing someone to feel unsafe, uncomfortable, or humiliated.
- Intimidation: Actions meant to instill fear digitally or physically.
- Displays of Offensive Objects: The act of sharing, showing, or placing items in a way that can emotionally harm others. This may include racist symbols, violent imagery, or discriminatory slogans.
Cyber Harassment vs Cyberbullying
Cyber harassment and cyberbullying are often used interchangeably. They share many similarities in legal and everyday contexts. However, cyberbullying is commonly used in youth-related environments and to refer to minors. On the other hand, cyber harassment typically refers to people of all ages and is more commonly used in a criminal context.
What Should I Do if I’m Being Harassed Online?
If you’re being harassed by someone online, it’s best not to engage with them. Make it clear to them that their behavior is unwelcome, but avoid any further communication. Then, your priority should shift immediately to documentation. This information will be critical when you report the incident. It includes:
- The name or account information of your harasser
- The messages or interactions that are causing you distress
- Timestamps of when the harassment occurred
It’s also important to mention that our experts advise against blocking the harasser. This may seem like the best way to cut them off, but blocking comes with the risk of deleting evidence. You should cease communication and mute the user if the option is available, but leave them unblocked until you’ve completed your investigation.
Where and How to Report Online Harassment?
There are several channels available for reporting cyber harassment, and using more than one often leads to better outcomes. Each plays a different role in stopping the abuse. Our team recommends the following steps to report online harassment, notify the proper authorities, and hold the perpetrator accountable.
Step-by-Step Guide to Reporting Online Harassment
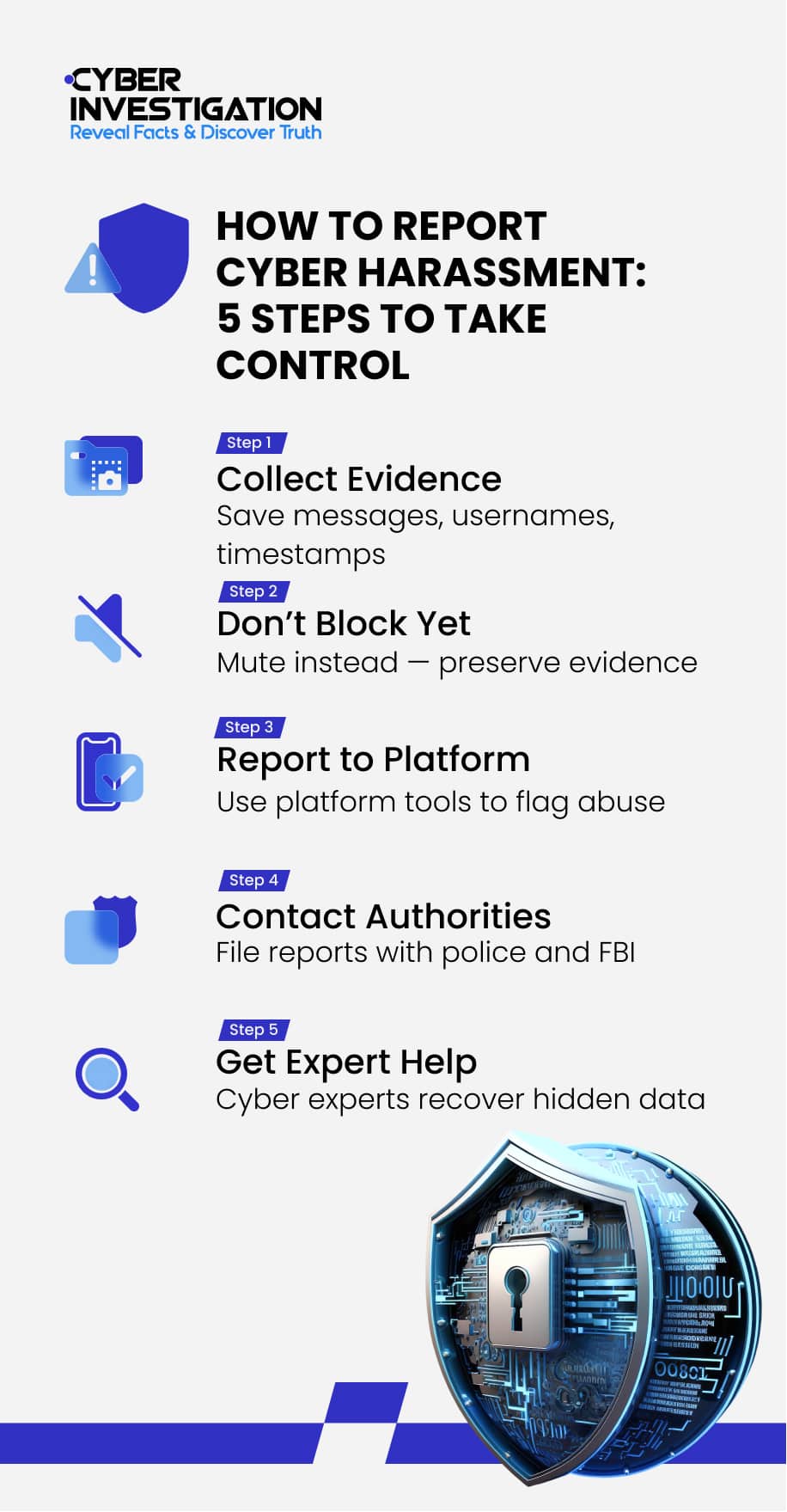
To recap what we’ve just covered, here is a clear and concise outline of the cyber harassment reporting process:
- Collect all evidence. Store your documented proof in a secure place you will be able to access without issue. Assign descriptive names to the screenshots that will allow you to recognize the file. Add the time and date to the file name to help chronologize your evidence.
- Report to the platform. Administrators can remove content and punish perpetrators.
- Notify law enforcement. Inform both your local and national agencies.
- Consider professional help. They can gather evidence to support your reports.
Depending on the nature of the harassment, you may be able to pursue legal action against your harasser. These include court-ordered protections, civil suits, and criminal charges. You should consult a lawyer to discuss your options and the laws around harassment in your area.
Report to the Online Platform
Each platform has a slightly different way to report users or shared content. There is typically an options menu near profiles and content that provides options like “Report” or “Flag.” To find out how this is done on a specific platform, visit their help and safety center. These reports are reviewed by the platform’s administrators. If they determine a violation has occurred, the user may face consequences like suspension and permanent removal.
The following are instructions on how to report harassment on popular online platforms:
- Meta (Facebook/Instagram): Tap the three-dot menu, select “Report,” choose “Bullying or Harassment,” follow the prompts, and submit your report.
- X (formerly Twitter): Click on the three-dot menu, select “Report,” choose “Abusive Behavior or Harassment,” provide additional details if prompted, and submit the report.
- TikTok: Press and hold the video or go to the user’s profile, tap “Report,” select “Harassment or Bullying,” follow the steps, and submit.
- YouTube: Click the three-dot menu next to a comment or video, select “Report,” choose “Harassment and Cyberbullying,” and submit the report.
Report to Law Enforcement
- Report to your local police. You can file a police report by gathering your evidence and heading to your local station. You may also be able to do it over the phone or online. Provide as much detail as you can to construct the most accurate timeline of events. If you feel an immediate risk to your safety, contact 9-1-1 for a harassment complaint.
- Report to the FBI. You can either file a report through the Internet Crime Complaint Center (IC3) or visit your nearest FBI field office. If the harassment includes more serious federal crimes, such as violent claims and interstate criminal communication, send a harassment complaint to tips.fbi.gov.
Consider Professional Help
It could be beneficial to enlist the services of a reputable cybersecurity firm to help deal with online harassment. These firms have access to proprietary technology and can employ advanced digital forensics techniques to uncover evidence.
Every online interaction leaves a trail of code. Every file that is shared contains metadata that discloses information like creation date, devices used, and the region of origin. Cybersecurity professionals and electronic harassment investigators know how to locate and extract this information to support efforts to identify the perpetrator.
Additional Resources for Victims of Cyber Harassment
There are also organizations that victims can turn to for guidance, emotional support, and an ear to listen. This can be just as important for recovery as holding the perpetrator accountable. Victims of cyber harassment are faced with a lot of complex emotions that can be hard to sift through on your own. Consider reaching out to these resources for harassment help.
- 988 Crisis Lifeline. This helpline runs 24/7 for anyone dealing with mental health struggles, emotional turmoil, substance abuse issues, or any other crisis.
- Crisis Text Line. Similar to the 988 lifeline, this service allows users to connect with crisis counselors by texting “HOME” to 741741.
- Online Harassment Field Manual. This guide provides concrete strategies to help internet users keep themselves safe from online abuse. The manual is tailored especially for groups that are disproportionately targeted but is universally helpful.
Legal Options for Victims
Depending on the nature of the harassment, you may be able to pursue legal action against your harasser. These include court-ordered protections, civil suits, and criminal charges. You should consult a lawyer to discuss your options and the laws around harassment in your area.
Legal action becomes more practical and effective when the perpetrator is identified, which is why evidence collection and digital investigations are critical to identifying the harasser.
Best Practices After Reporting Harassment on Social Media
Social media platforms provide multiple tools to deal with harassment, and using them correctly makes a significant difference. The goal is not just to stop the immediate interaction, but also to preserve evidence, reduce exposure, and increase the chances of enforcement action.
Mute or Restrict to Reduce Immediate Impact
If the harassment is ongoing but not yet escalated, use mute or restrict features instead of immediate blocking.
These tools:
- Hide messages or comments without alerting the harasser
- Prevent further emotional escalation
- Allow you to continue monitoring and documenting behavior
This approach is especially useful during the evidence collection phase.
Block the User After a Proper Investigation
Blocking is an effective way to stop direct interaction, but timing matters.
Once you have:
- Captured screenshots and timestamps
- Documented repeated behavior
- Reported the incident
- Conducted a professional investigation
You can block the user to prevent further contact. Most platforms allow blocking from the user profile or settings menu. Blocking removes their ability to message, view, or interact with your content.
However, blocking too early can result in loss of access to messages or content, which may weaken your report.
Avoid Engagement or Retaliation
Do not respond emotionally or engage in arguments. Harassers often seek reactions, and engagement can escalate the situation.
Official cyber safety guidance consistently recommends:
- Not replying to abusive messages
- Avoiding public arguments
- Staying focused on documentation and reporting
If you must respond, keep it factual and minimal.
Report Repeated Incidents Consistently
One report is often not enough. Platforms rely heavily on user reports to identify patterns of abuse.
If harassment continues:
- Report every new incident
- Reference previous reports where possible
- Keep your evidence updated
Repeated reporting increases the likelihood of stronger enforcement actions, including account suspension.
Strengthen Privacy and Account Controls
While reporting handles the current issue, prevention reduces future risk.
Adjust settings to:
- Limit who can message or tag you
- Restrict profile visibility to trusted users
- Remove or hide personal information
Many platforms also allow you to filter keywords or automatically hide offensive comments.
How Online Harassers Think: Psychology and Motivation
Online harassers are not all the same, but they use similar tactics to target victims and for similar reasons. There is a mix of social dynamics and psychological motivations that can contribute to the behavior of these criminals. The digital era has only increased the number of online harassers and amplified their reach.
Below are some of the common motivations and patterns that have been observed in online harassers. By understanding these motivations, victims can respond more strategically rather than emotionally.
- Using anonymity. The internet allows bad actors to operate anonymously from all around the world. Their anonymity not only protects criminals from being held accountable for their actions, but it also encourages them to do and say things they wouldn’t in person.
- Wanting power or control. Perpetrators typically desire power or control over others. They use cyber harassment to intimidate specific targets.
- Feeling insecure. Feeling threatened by the positive attributes of others, they can operate from a place of insecurity and may target individuals to tear others down.
- Lacking empathy. Perpetrators often harass victims online without considering the real-world implications of their actions. By focusing on the digital interactions, they dehumanize their targets and see them only as usernames.
- Attention-seeking behavior. Cyber harassment typically stems from something missing in the culprit’s personal life. Harassers may want attention or a sense of power and gain that comes from targeting someone online.
- Revenge against someone they know personally. Some cyber harassers know their targets in real life. It may be a former partner, friend, or acquaintance that has a vendetta against the victim.
How to Assess the Threat Level
Cyber harassment carries different levels of risk and threat. That’s why proper threat assessment is very important for deciding your next steps.
Low-level harassment:
- One-time insults or trolling
- No personal information involved
Moderate risk:
- Repeated messaging
- Targeted harassment campaigns
High risk:
- Threats of violence
- Doxxing or exposure of personal data
- Stalking behavior across platforms
High-risk harassment scenarios must be reported immediately to law enforcement and qualified cybersecurity professionals.
How to Protect Yourself from Cyber Harassment
Harassers are motivated by a range of incentives such as power, revenge, or prejudice. They can target someone obsessively based on the briefest of moments. Anyone with an online presence can become a target for online harassment. The reason for this targeting can stem from something that occurred in real life or over the internet.
However, there are ways to make it more challenging for perpetrators to digitally harass you and minimize the risk of becoming a victim. Knowing how to avoid online harassment is essential for safe internet use.
Key prevention strategies include:
- Strengthen privacy settings across all platforms. The first step to protecting yourself digitally is to limit your exposure to cybercriminals. You can do this by making your social media accounts private, allowing only your followers or friends to see your posts.
- Avoid sharing sensitive personal information publicly. Harassers and cyber stalkers will use any information about you to target you. Names, locations, email addresses, and phone numbers can all perpetuate cyber harassment. Consequently, it’s best to stay cautious when making posts and drafting your profile bios.
- Use strong, unique passwords for every account. Strengthening the security on your accounts and devices protects your information from the perpetrator. Make sure your passwords are complex and unique to each of your accounts. You can also check to see if your password has been exposed in a corporate data breach.
- Enable two-factor authentication (2FA). Two-factor authentication (2FA) is another tool users can employ to secure their accounts even in the case of an exposed password. You can enable the setting on most social media networks and dating platforms.
- Audit followers and remove unknown accounts. Make sure to audit the list of people who follow you and remove anyone you don’t know well.
- Avoid engaging with trolls or suspicious profiles. Bad actors may send an unsolicited message to you under a fake profile, luring you into their web. Any engagement with these profiles only encourages the perpetrator to continue their behavior. Making it more difficult for the harasser to get in touch with you can lead to disinterest, prompting them to move onto other targets.
If You’re Experiencing Cyber Harassment, Take Action Now
If you are facing online harassment, you don’t have to handle it alone. And if the perpetrator is hiding behind anonymity, identifying them is often the key to stopping the abuse.
Cyber Investigation can help you uncover evidence, organize your case, and identify your harasser using advanced digital forensics. Our team works with complete confidentiality to protect your privacy while helping you take control of the situation.
If you are ready to stop cyber harassment and hold the offender accountable, reach out today to speak with an expert.
Frequently Asked Questions
Can cyber harassment be traced?
Yes. Digital forensics experts can analyze metadata, IP logs, and behavioral patterns to identify anonymous harassers.
Should I block someone who is harassing me?
No. Avoid blocking until you have collected all necessary evidence, as blocking may remove access to important proof.
Is cyber harassment a crime?
Yes. Depending on severity, it can lead to criminal charges such as stalking, threats, or defamation.
What if the harasser is anonymous?
Anonymous users can be traced through technical investigation methods and cooperation from online platforms.